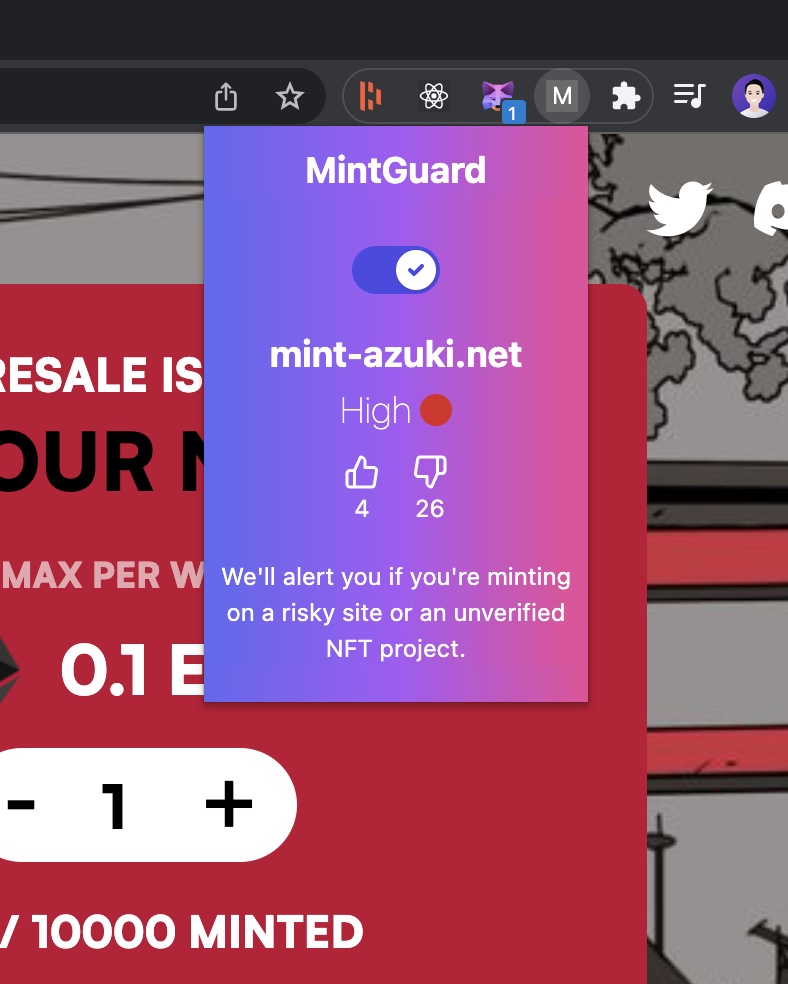
MintGuard
Anti-scam web extension to detect NFT scam sites and scammy addresses
Project Description
https://dennisdang.notion.site/MintGuard-roadtoweb3-hackathon-submission-50aba94088e84bf683c72861ccd59bc1
Many have gotten scammed and sent transactions on a scammy site in the heat of it, rushing to buy an NFT or tokens. Can we we make the web3 experience safer by optionally allowing users to slow down?
Let's build a web extension that can verify contract addresses paired with their HTTP domain sites. There are numerous heuristics we can look to as well, but for MVP, we'll start with basic wallet-address and domain pairing.
Additionally, I can review addresses and distill a risk score with the Covalent API based on NFT activity and presence of token IDs.
How it's Made
I spun up two codebases to develop the web extension and a typical Nodejs express server.
The web extension is the frontend from which users can toggle on and off safe mode. It's a React UI, following typical web extension development. My first time really digging into web extension development. The challenges of learning a new web API and especially learning how background scripts, content scripts, and the browser action UI communicate with one another has been fun.
The hard part was figuring out how to get the "to" address that a user attempts to send a transaction to. From there, it's a simpler matter of taking that address, passing it into the web extension, calling our API there to return a risk score. However, this step of programmatically reading the address is still TBD. For MVP, we simply allow users to paste their target address in. I was digging into the Metamask Flask work, a developer-oriented nightly build of Metamask. There's a Snaps API that may allow me to build an API to read request txns before they're sent. I also considered customizing the metamask web extension myself to emit a new custom event on txn request.
The risk score is a simple 0-100, 100 being certainly risky. It's computed based on some static logic around Covalent's API.
The API is deployed on Fly.io.